I Got Hacked: Inside a Discord Social Engineering Campaign Built Around a Fake Minecraft Launcher
On April 16, 2026, I accepted a Discord friend request from a random account with no shared friends and no shared servers.
Normally, that would be a red flag. But I have multiple public profiles, I help people in technical threads across the internet, and I publish security research. It is not unusual for strangers to reach out to me. Sometimes they want help with tooling. Sometimes they are trying to reproduce a bug. Sometimes they have a half-written question they do not know how to ask yet. That background made the request feel unusual, but not impossible.
I assumed this was probably another person who had seen one of my previous write-ups and wanted help.
Two days later, it turned into a live social engineering operation, a malware analysis session, and an incident response exercise all at once.
What makes incidents like this dangerous is not technical sophistication alone. It is timing, tone, and patience. A lot of people still imagine malware delivery as something loud and obvious: a broken English email, a fake invoice, a sketchy attachment from nowhere. That still exists. But increasingly, what actually works is something much more human. A conversation. A little flirtation. A little urgency. A little pressure. A file that seems almost plausible because it arrives at the end of a social interaction rather than at the beginning.
That is exactly what happened here.
April 16, 2026: The Friend Request
The first step was almost boring in how ordinary it looked.
A random Discord user sent me a friend request. No overlap. No context. No mutuals. No shared communities. No obvious sign of why this account had found me at all.
Still, because of the kind of public work I do, that alone was not enough to treat it as malicious. People find me through GitHub, blog posts, old research threads, forum replies, and random social circles that only become clear later. I accepted it and moved on.
Nothing happened immediately.
That delay matters. A request followed by silence feels less threatening than a request followed by a pitch. There is no instant ask, no obvious scam script, no pressure. Just a new contact sitting in your list long enough to feel normal. Social engineering often works best when it avoids looking like social engineering.
April 18, 2026: The Setup Starts
On April 18, 2026, the account finally sent a message: selam.
That single word was enough to tell me almost nothing and also everything. It was casual. Low-friction. Easy to answer. Designed to get the conversation moving without giving me any useful context in return.
Instead of answering normally, I replied with a small secret reference from one of my previous research threads to see whether this person had actually found me through my work. It was a simple test. If she had seen the research, she would understand the reference or at least react like someone who knew why she had contacted me.
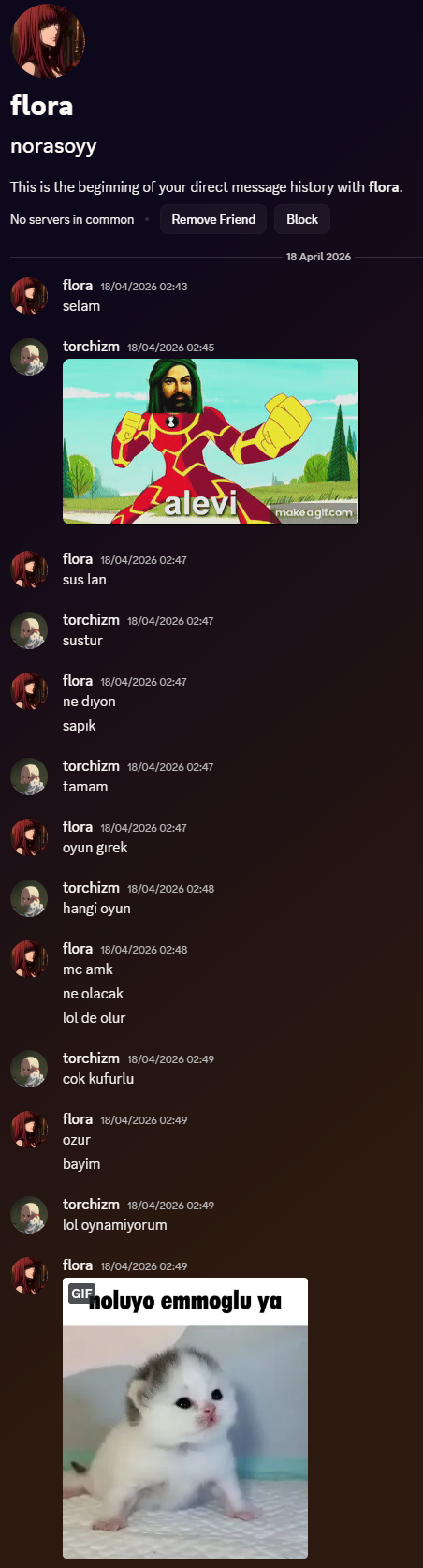
The answer never came. There was no sign she knew anything about my research at all.
Then the conversation pivoted.
She asked if I wanted to play games with her. That was the moment my suspicion level went up. The conversation had skipped the entire "why are you messaging me?" phase and jumped directly into an invitation.
I asked her age. She said she was 18.
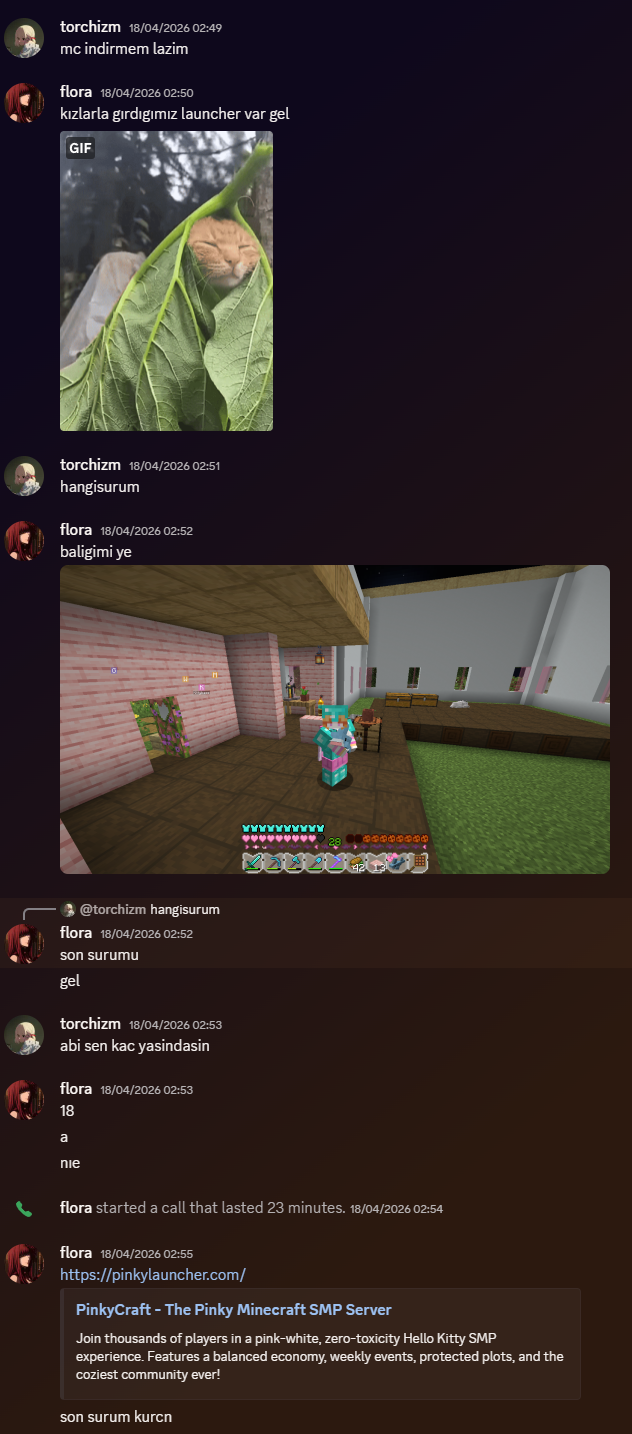
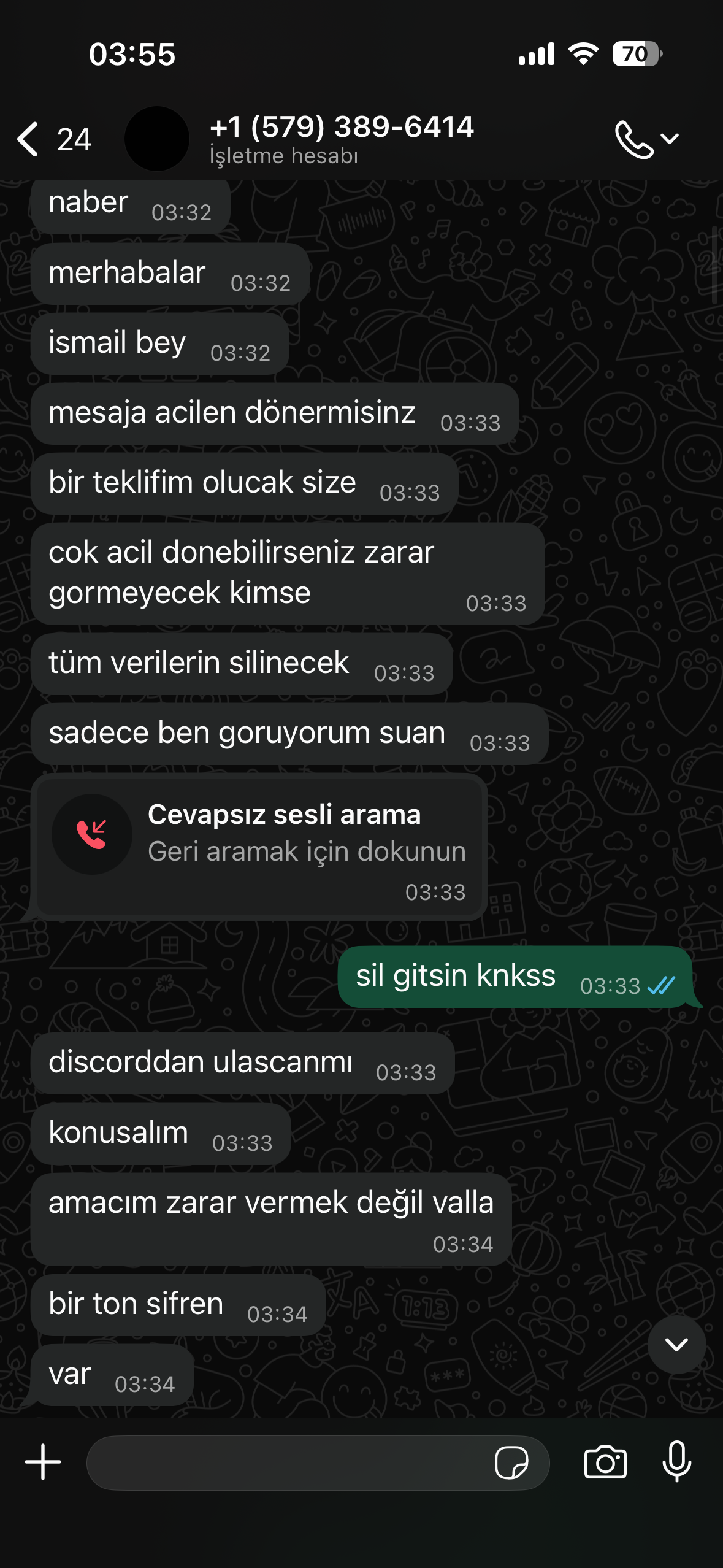
Then she sent random Minecraft screenshots and dropped a link: pinkylauncher[.]com.
That was the first hard technical signal.
I checked the domain's registrar history and age on SecurityTrails. The domain had been registered only 17 days earlier.
So I pushed back gently and asked whether the server was new.
She said she had been playing on it for two months.
That contradiction was enough for me. At that point the story stopped being fragile and started breaking.
From there, the social side of the operation became easier to read. The "person" on the other side wanted very specific outcomes:
- Keep the conversation casual.
- Create emotional momentum.
- Get me to trust a file.
- Get me to run it fast.
At that point, I was no longer talking to a random person on Discord. I was dealing with someone trying to move me toward a binary they urgently wanted me to execute.
Building a Safe Detonation Environment
Before touching the file, I moved the entire interaction into a disposable environment.
I launched a fresh Windows 11 instance with Windows Sandbox, installed Discord and Chrome inside it, and logged in with dummy accounts. I wanted a controlled environment where I could observe the behavior of the launcher without putting any real identities or sessions at risk.
That setup decision was the single most important defensive move in the entire story.
If I had treated the conversation casually for even a few more minutes and run the file on a real desktop with live sessions, the rest of this post would be very different. The launcher was clearly designed for speed. This was not the kind of malware that waits for a long dwell time before touching browser or messaging state. It was meant to get in, take what it could, and move fast enough that the operator could start leveraging the compromise while the victim was still confused.
While the social engineering pressure continued in the background, I started triage on the sample itself.
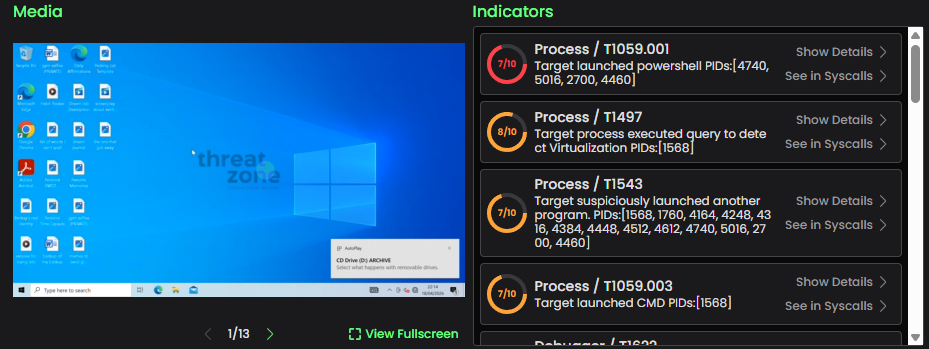
I uploaded the file to threat.zone for a quick dynamic pass. I was not looking for a courtroom-grade malware report yet. I wanted the fast answers first: does it reach out, does it unpack anything suspicious, does it exhibit credential-focused behavior, and is it likely to be commodity junk or a tailored build?
At the same time, I looked at the launcher's website source. There, I found enough backend plumbing to know I was not looking at some amateur prank. The site did not read like a harmless fan page thrown together for a private Minecraft server. It looked like infrastructure attached to collection and notification.
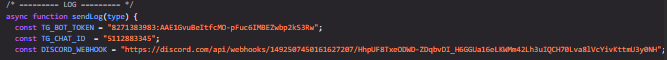
I also confirmed that the executable was an Electron-based application. That mattered because Electron gives attackers a convenient cross-platform packaging story and a JavaScript-heavy codebase that is easy to obfuscate, bundle, and ship quickly. After unpacking the archive structure, it became clear the logic had been deliberately hidden behind JavaScript obfuscation layers and compiled bytecode.
At that point, a deep reverse engineering pass would have been interesting, but it was not yet necessary. I already had what I needed:
- the launcher was not trustworthy,
- the delivery path was deceptive,
- the infrastructure behind it appeared to be set up for credential theft and collection,
- and the person pressuring me on Discord was working in sync with that infrastructure.
That last point is important. A lot of malicious binaries float around without a live operator on the other end. This did not feel like that. This felt like an active human-in-the-loop theft pipeline.
I also found signs that the operation was receiving stolen Discord account material and browser-derived data from Turkish users. The victim profile looked localized. The collection path looked active. The scale looked larger than a single scammer improvising with one throwaway file.

That changed the nature of the case. This was no longer just "someone sent me a shady Minecraft launcher." It looked like an active theft pipeline.
Social Engineering Under Pressure
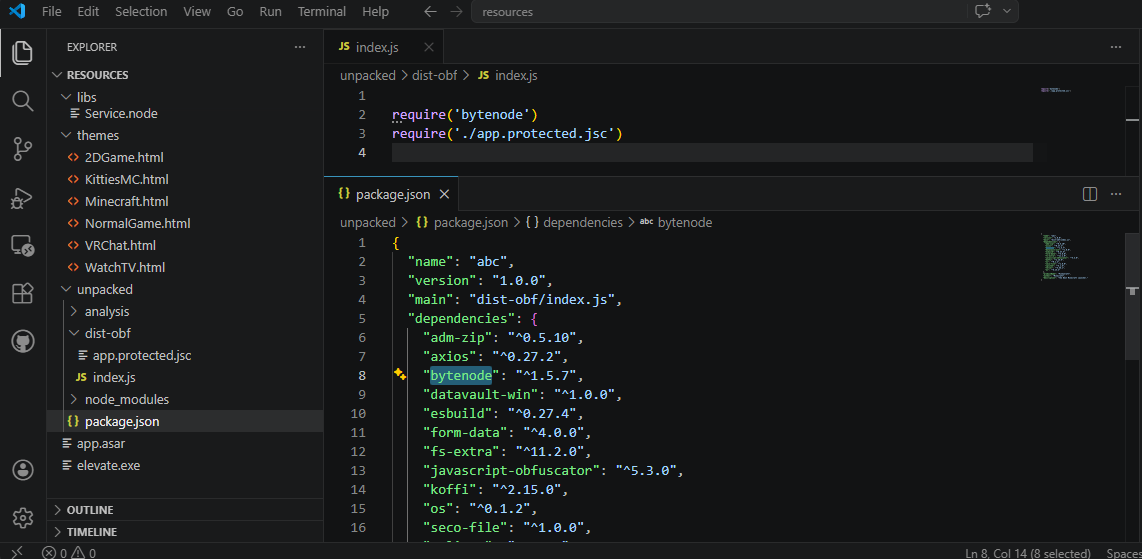
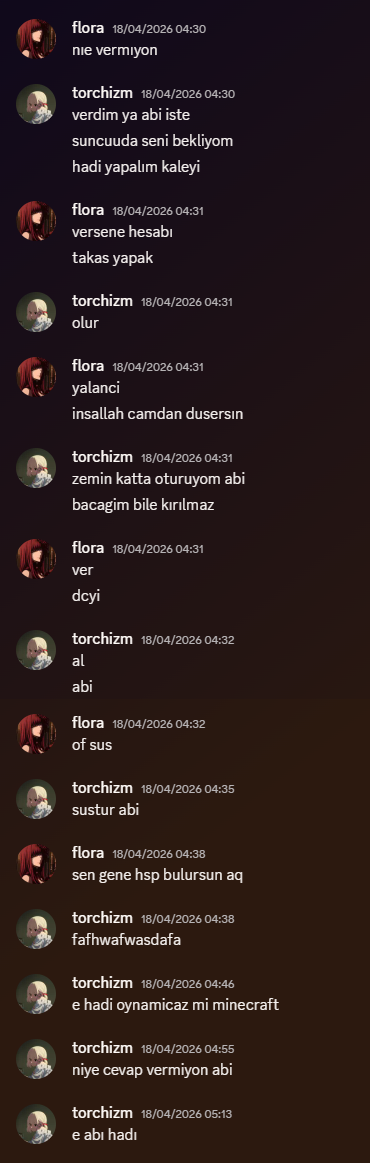
While I was analyzing the infrastructure, the Discord conversation kept escalating.
She wanted me to install the launcher immediately. She kept pushing me to join her in Minecraft. She asked where I lived, what I liked, and eventually claimed she wanted to meet me in person in Ankara.
The pace was the giveaway: urgency, intimacy, and pressure, all at the same time.
That combination is not accidental. It is a psychological compression technique. If the operator can make you feel curious, flattered, slightly rushed, and a little socially obligated all at once, your normal verification habits start to erode. You stop thinking like a defender and start thinking like a participant in a conversation.
Then came the request that made the objective completely obvious.
She asked me to share my screen so she could "help" me with the installation steps.
That is classic social engineering. The goal was not just to get the malware executed. It was to control the execution path, reduce hesitation, and make sure the payload reached the point where it could access whatever it needed.
Screen-sharing pressure also serves another purpose: it gives the attacker immediate feedback. If something fails, they can guide the victim around the failure. If the victim hesitates, they can push harder. If Discord or Chrome closes and the victim looks confused, they can react in real time.
In other words, they were not merely trying to deliver malware. They were trying to supervise compromise.
The Moment I Ran It
Once the sandbox was ready, I executed the launcher inside the disposable environment.
Chrome and Discord disappeared almost immediately.
That told me two things right away. First, the malware was doing something active and fast rather than waiting passively. Second, whoever was on the other end was watching closely enough to notice the state change in real time.
The speed matters. A fast-close on browser and chat applications strongly suggests the operator wanted control over active sessions, stored credentials, and any other reachable data without giving the victim much time to react. In practical terms, it felt less like a random infected executable and more like a purpose-built tool for account theft.
She immediately asked why I was still in the Discord call if Discord was supposedly closed.
For a brief moment, even inside a sandbox, the real-time nature of the attack hit harder than I expected. Seeing malicious behavior in analysis is one thing. Watching the operator react to it live is something else.
I told her it was bugging out and exited the conversation.
Fortunately for me, they had no idea they were trying to socially engineer someone who works in cybersecurity and was already dissecting their entire playbook.
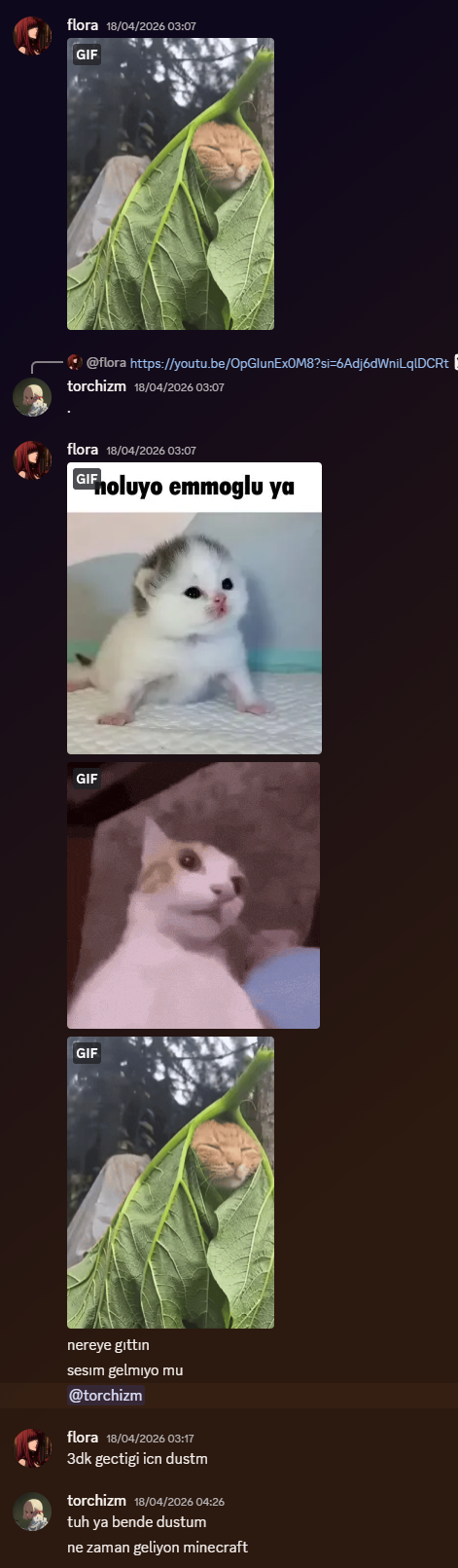
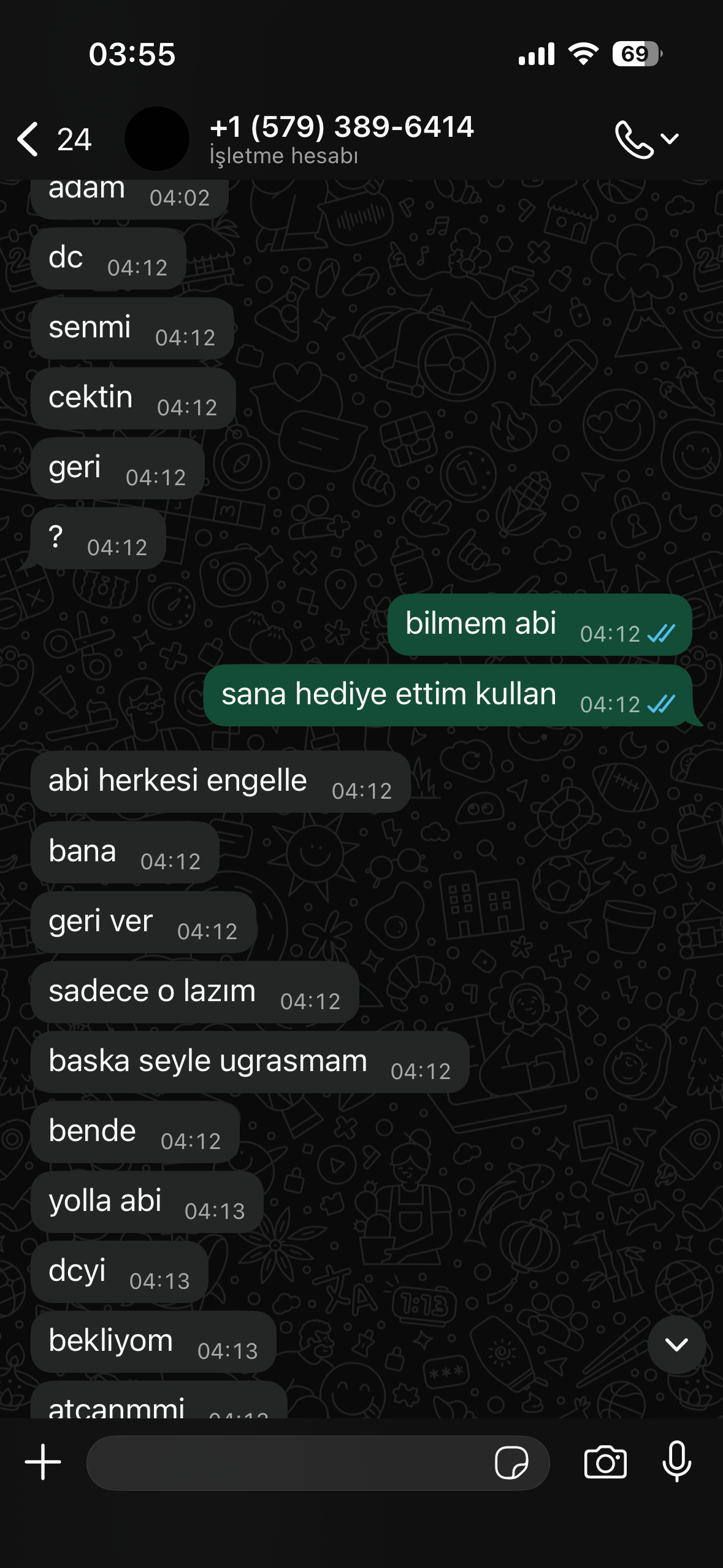
The WhatsApp Pivot
About two minutes later, I received a WhatsApp message from a Canadian number.
The message, in Turkish, was essentially: "Hello Ismail, all data will be deleted. If you return urgently, nobody will be harmed."
My response was simple: "Delete it, then."
That message is worth pausing on because it reveals a lot about how these operators think.
The threat was vague on purpose. It did not explain what data. It did not explain what "harm" meant. It only tried to trigger urgency. The idea was not to persuade me logically. The idea was to destabilize me emotionally, get me talking, and regain initiative.
He claimed he did not want to cause harm. Then he sent me screenshots from chats tied to the dummy Discord account, clearly trying to prove access and establish control. It was intimidation, but it was also sloppy. The attackers were moving fast, improvising, and exposing more of their operation than they seemed to realize.
By that point, the dummy Google and Discord accounts had already been pivoted. Recovery settings were changed. Passwords were changed. The point was not persistence on me personally. The point was account capture and monetization.
That is another useful lesson. In a lot of criminal workflows, the attacker does not need long-term stealth. They need speed and transferability. If they can change enough of the recovery surface quickly enough, they can turn an account into inventory.
When the Attacker Started Making Mistakes
The operation looked coordinated, but the operator I was dealing with was careless.
During the account activity and follow-on interaction, he exposed device and network information that gave me visibility into who was actually behind the screen. He was not even using a VPN. The only protection he seemed to rely on was a Discord-access workaround.
That was not the only surprise.
Once I kept him talking, he started volunteering information.
Some of it may have been exaggeration, and I want to be clear about that. The details below are attacker claims gathered during recorded conversations unless independently verifiable.
According to him, there were roughly 120 people involved behind the scenes, focused on stealing aged Discord accounts with badges and selling them for anywhere between $50 and $1200 in cryptocurrency. He claimed he personally earned around $200 per week for participating.
Then he dropped the detail that changed the tone of the entire exchange.
He said he was 17 years old and still in high school.
He also claimed that the malware tooling was being produced by a friend using AI-assisted coding tools.
That does not make the operation sophisticated in a classical sense, but it does make it scalable. When low-skill operators can combine social engineering, packaged malware, and disposable infrastructure, the barrier to entry drops fast.
The important point here is not whether every word he said was true. Attackers lie, brag, and mythologize themselves constantly. The important point is that the ecosystem he described is plausible: stolen accounts treated like commodities, young operators handling outreach and execution, and malware builds assembled quickly enough that the social engineering layer matters more than the code quality.
That model fits what I was seeing much better than the fantasy of some lone genius operator. It looked more like a low-discipline revenue machine.
Defensive Response and Containment
At that point, my priorities were straightforward: contain the blast radius, recover the disposable accounts, preserve evidence, isolate the environment, and make the attackers less certain about what they had actually captured.
I recovered control of the affected test accounts and continued recording the conversations. I kept everything inside the disposable environment and treated the interaction as evidence first, ego second.
That distinction matters. When you realize you have visibility into an attacker, there is a strong temptation to start treating the moment like a game. But the useful work in an incident is usually boring: account recovery, state verification, evidence preservation, scoping, timestamps, and making sure you can reconstruct the sequence later.
I also disrupted part of their telemetry stream by feeding it controlled junk data shaped like the material they appeared to be collecting. The purpose was not revenge. It was confusion. If they wanted a clean signal, I wanted them spending time on noise.
I am intentionally leaving the exact recovery path, access method, and disruption mechanics out of this post. The defensive lesson matters. The step-by-step tradecraft does not belong here.
What I can say is this: once an attacker believes they have a stable stream of useful data, even small amounts of believable noise can force them to spend time validating, rechecking, and second-guessing what is real. In a criminal workflow built on throughput, uncertainty is friction.
The Final Conversation
After more threats, I called him on WhatsApp.
I asked where he lived. He said Ankara.
Then I asked why I was seeing him in Izmir.
The silence that followed was one of the few honest moments in the entire exchange.
He stopped threatening me for a second and started asking how I knew anything at all.
I let him sit in that confusion. I played along, acted impressed, and kept him talking. At one point I even put music on in the background and let the discomfort do part of the work for me. I was tired by then, but I had also reached that peculiar point in an incident where the fear is gone and curiosity takes over.
The more he talked, the more the image sharpened: not a mastermind, not a hardened operator, but a teenager caught inside a profitable little ecosystem of stolen accounts, copied malware components, and bad operational security.
There is a strange emotional texture to moments like that. On one side, you are dealing with real malicious behavior and real victims. On the other, you are suddenly hearing the voice of someone who sounds much smaller than the damage they are helping cause. That does not reduce responsibility. But it does strip away the theatrical aura these people try so hard to project.
Eventually I told him I was going to sleep.
Then I reopened Discord and messaged the original account again. She had already understood that I had recovered everything. The tone changed immediately from manipulation to swearing and threats. After that, she stopped replying.
That sudden shift was probably the cleanest indicator of all. The flirting, friendliness, and fake intimacy vanished the moment the operation stopped working. None of it had ever been personal. It was just another interface.
What Defenders Should Take Away From This
There are a few lessons here that matter more than the theatrics.
1. Unexpected Discord friend requests are not harmless
If there are no shared friends, no shared servers, and no clear context, assume nothing. Social engineering often starts with a tiny ask and a normal-looking message. The first sign of danger is often not the link. It is the lack of a believable reason for contact.
2. Gaming launchers are high-risk binaries
Anything marketed as a "private server launcher," custom modpack installer, or unofficial game helper deserves the same suspicion you would give any unsigned executable from a fresh domain. Gaming communities normalize downloading random helpers far more than most users realize, which makes them an ideal social engineering surface.
3. Infrastructure age matters
A domain that appeared 17 days ago should not align with a story about two months of normal use. Small contradictions are often the first reliable signal. Attackers can fake screenshots, personas, and confidence more easily than they can fake infrastructure history.
4. Disposable environments change everything
Windows Sandbox gave me a clean detonation chamber. If you do malware analysis, fraud research, or incident response, disposable environments are not optional luxuries. They are basic safety equipment. In this case, that one decision separated a controlled experiment from a real compromise.
5. Never mix real accounts with exploratory work
Dummy accounts turned this from a potential personal compromise into a controlled observation opportunity. Test identities should stay separate from your real communication, email, and browser sessions. If you research adversarial ecosystems, account hygiene is not paranoia. It is operational discipline.
6. Social engineers press on emotion, not logic
Urgency. Flirting. Personal questions. Requests to meet. Pressure to share your screen. Pressure to install now. None of that was random. It was a sequence designed to compress judgment. People rarely get manipulated because they lose technical knowledge. They get manipulated because the situation is engineered to make technical thinking feel socially inconvenient.
Closing Thoughts
This incident started with a Discord friend request and a fake Minecraft launcher. It ended with a clearer view into a small but active account-theft ecosystem, recorded conversations full of attacker admissions, evidence tied to real operator mistakes, and a much sharper reminder of how modern social engineering actually works.
The technical side mattered, but the human side mattered more. The fake persona. The patient delay. The casual message. The contradictory cover story. The pressure to hurry. The attempt to move from chat into supervised execution. The switch from charm to threats the moment control slipped.
That is the part defenders should remember.
They thought they were pushing a victim into a hurry.
What they did not realize was that, by the end, I was no longer the one being observed.
And they had no idea the full package was about to be handed to the authorities.